IoT Device Security: Architecting Robust Defenses in the Electronics Sector
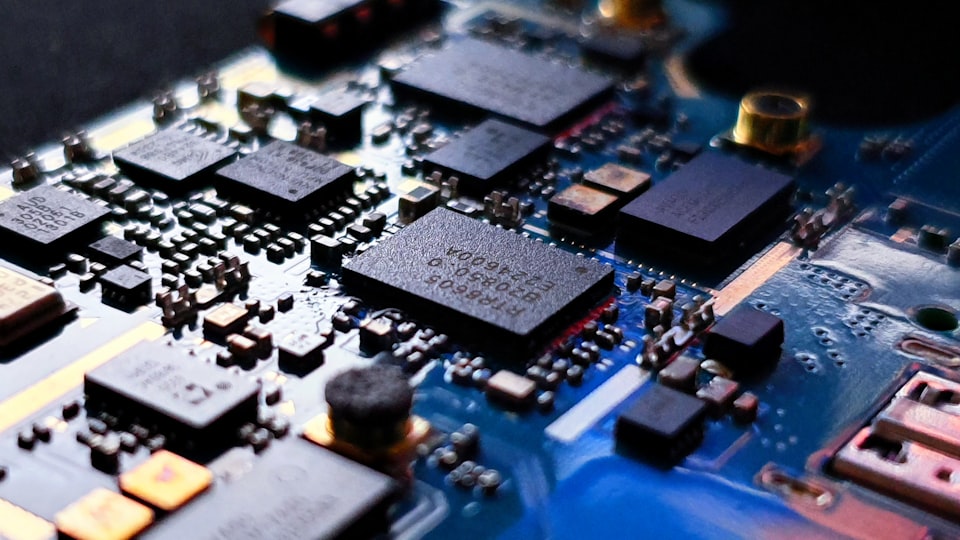
The electronics industry, at the forefront of this technological advancement, faces growing threats to IoT. The solution lies in exploring the device's core through embedded security solutions, ensuring safety while embracing innovation.
Embedded Security: A Proactive Approach to IoT Protection
At its heart, embedded security means integrating safety mechanisms directly into the very fabric of secure IoT devices. This approach ensures that the device's protection isn't just an added layer but a foundational part of its design.
Secure Boot Process
Each time an Internet of Things (IoT) device powers on, it should go through a process to verify the authenticity of its software. This process ensures that only code that has been verified and approved is allowed to run on the device. By implementing this security measure, the device establishes a strong first line of defense against potential threats that may try to exploit its software.
Hardware-Based Shields
By incorporating advanced protective measures such as hardware security modules (HSM) directly onto the device, you ensure that robust IoT security solutions are embedded right from the initial stage of development. This not only enhances the overall security posture of the IoT ecosystem but also provides a solid foundation for safeguarding sensitive data and ensuring the integrity of connected devices. With the integration of HSMs, organizations can effectively mitigate risks associated with unauthorized access, tampering, and data breaches, thereby establishing a strong security framework that aligns with industry best practices and regulatory requirements.
Real-time Threat Monitoring
By utilizing advanced AI and machine learning directly on the device, we can successfully accomplish the goal of continuous Smart Device Security surveillance. This revolutionary approach enables your devices to proactively detect, analyze, and counteract potential threats, ensuring the utmost level of protection, even in offline scenarios where internet connectivity may be limited or completely unavailable.
Encrypted Channels
Every single data transaction, whether it is occurring within a device or being transferred to external networks, should be encrypted. It is of utmost importance to implement encryption protocols in order to safeguard the confidentiality and security of the data. By encrypting the data, even if it is intercepted by malicious individuals or unauthorized entities, it will be rendered incomprehensible and inaccessible to them, thus preserving the privacy and integrity of the information being transmitted.
Regular, Secure Updates
Given the constantly changing landscape of IoT threats, it is imperative that devices are equipped with the capability to securely receive and implement over-the-air (OTA) updates. This not only ensures their continued functionality but also enables them to stay ahead of emerging vulnerabilities and potential security breaches. By embracing this agility and adaptability, devices can effectively safeguard themselves against new and evolving threats, providing users with peace of mind and a more secure IoT ecosystem.
Exein Runtime: The Vanguard of Embedded Security
While the foundational principles of embedded security remain consistent, the tools and solutions at our disposal continue to evolve. One such state-of-the-art solution that showcases the advancement in this field is Exein Runtime. This cutting-edge technology, specifically designed for IoT, brings AI-based protection to the edge, revolutionizing the way we safeguard our devices.
The brilliance of Exein Runtime lies in its ability to harness the power of on-device machine learning. By leveraging this advanced technology, devices equipped with Exein Runtime gain the capability to actively monitor, detect, and counteract threats autonomously. This means that even in environments where internet connectivity is sporadic or non-existent, these devices can still provide robust security measures. This not only optimizes device performance but also ensures that devices, regardless of their inherent computational power, are always shielded from potential breaches.
In addition to its powerful security capabilities, Exein Runtime boasts a modular architecture that allows for seamless integration into a wide range of devices. This means that whether it's a smart home device, a wearable gadget, or an industrial machine, Exein Runtime can be easily incorporated without compromising device functionality or performance. This versatility ensures that state-of-the-art protection is accessible to a diverse array of devices, keeping them safe from emerging threats.
Exein Runtime represents a significant advancement in the field of embedded security. With its AI-based protection, autonomous threat detection, and seamless integration capabilities, it sets a new standard for device security in the IoT era.
Security professionals now can have peace of mind knowing that their devices are equipped with state-of-the-art security measures, even in challenging connectivity conditions.
The Future of Embedded Security in the Electronics Sector
As the electronics industry moves forward in technological innovation, it becomes more important than ever to prioritize security. In the past, the focus was often on delivering new features without considering the need for strong security. However, in today's landscape filled with advanced threats, we need to change our approach.
That's where embedded security comes in.
It's a proactive way of ensuring that devices have built-in protection from the start.
One of the tools that supports this approach is Exein Runtime. It's not just another security add-on, but a game-changer. It gives IoT devices the ability to not only react to threats but also anticipate and neutralize them. By integrating AI-driven protection strategies directly into devices, Exein Runtime raises the bar for security. It ensures constant protection against potential breaches.
The goal for the electronics industry is clear: to create a future where IoT devices combine intelligence with strong security. In this future, consumers won't have to sacrifice convenience for safety.
Every interaction with their devices, whether it's adjusting a smart thermostat or checking a connected security camera, will be based on trust. They'll know that their devices have been designed with their safety in mind.
Manufacturers also benefit greatly from this approach. Besides the obvious advantages of reduced vulnerability and financial implications of breaches, there's also a gain in reputation. They can proudly position themselves as pioneers who are committed to delivering original and secure products. Essentially, they'll be leading a new era where smart truly meets secure.




