Automotive Cybersecurity: Exposing Auto-System Vulnerabilities and Exein's Enterprise Countermeasures
In an age where technology is woven into the very fabric of our lives - and our vehicles - understanding how our automotive systems can be compromised and how to defend against these threats is more crucial than ever.
From engine controls to navigation systems, hackers have found various ways to intrude. We've created an infographic that illustrates these complex issues in an easy-to-digest format.
Take a visual journey with us into the inner workings of automotive system hacks and discover how Exein's pioneering cybersecurity solutions keep you a step ahead.
Infographic breakdown
Comprehensive Defense from Threat Detection to Fail-Safe Measures
With the proliferation of IoT devices, a new era of cybersecurity risks has emerged, requiring robust measures to safeguard sensitive data, critical infrastructure, and ensure the continuity of operations.
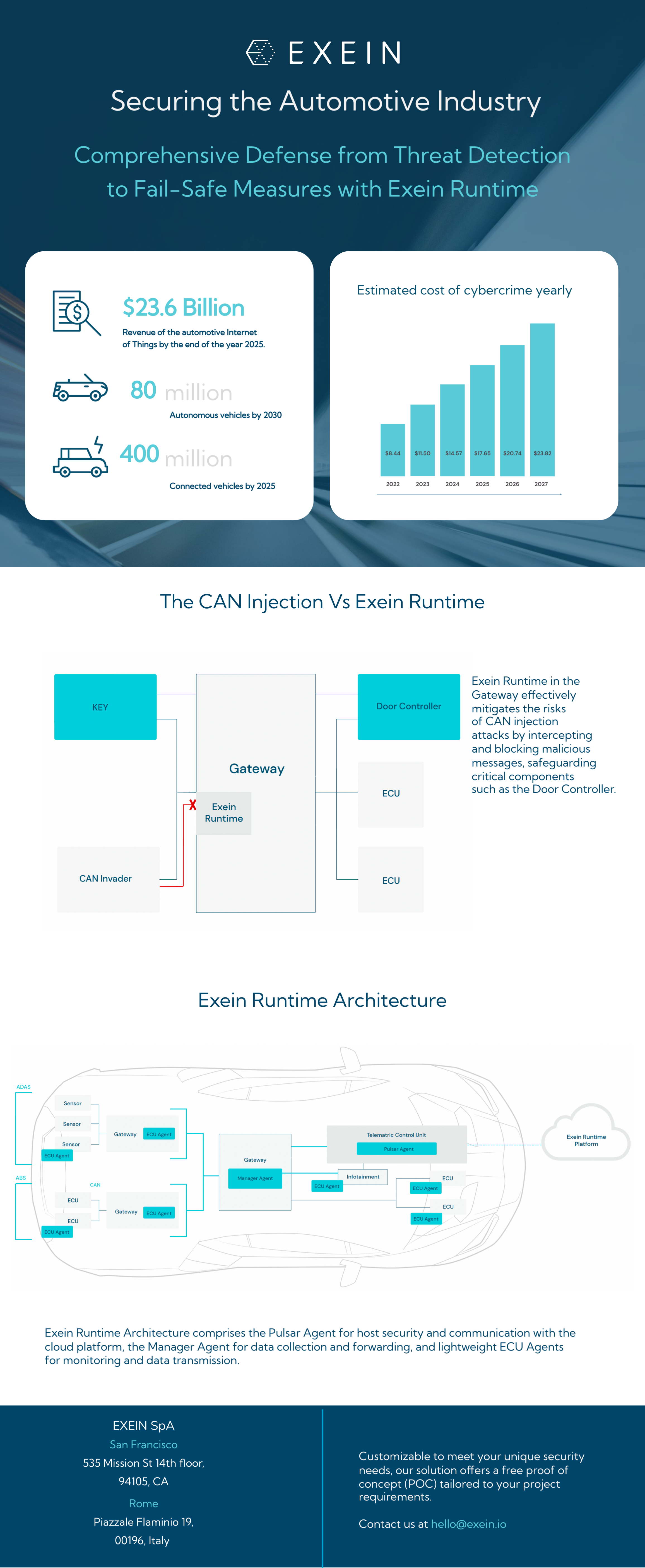
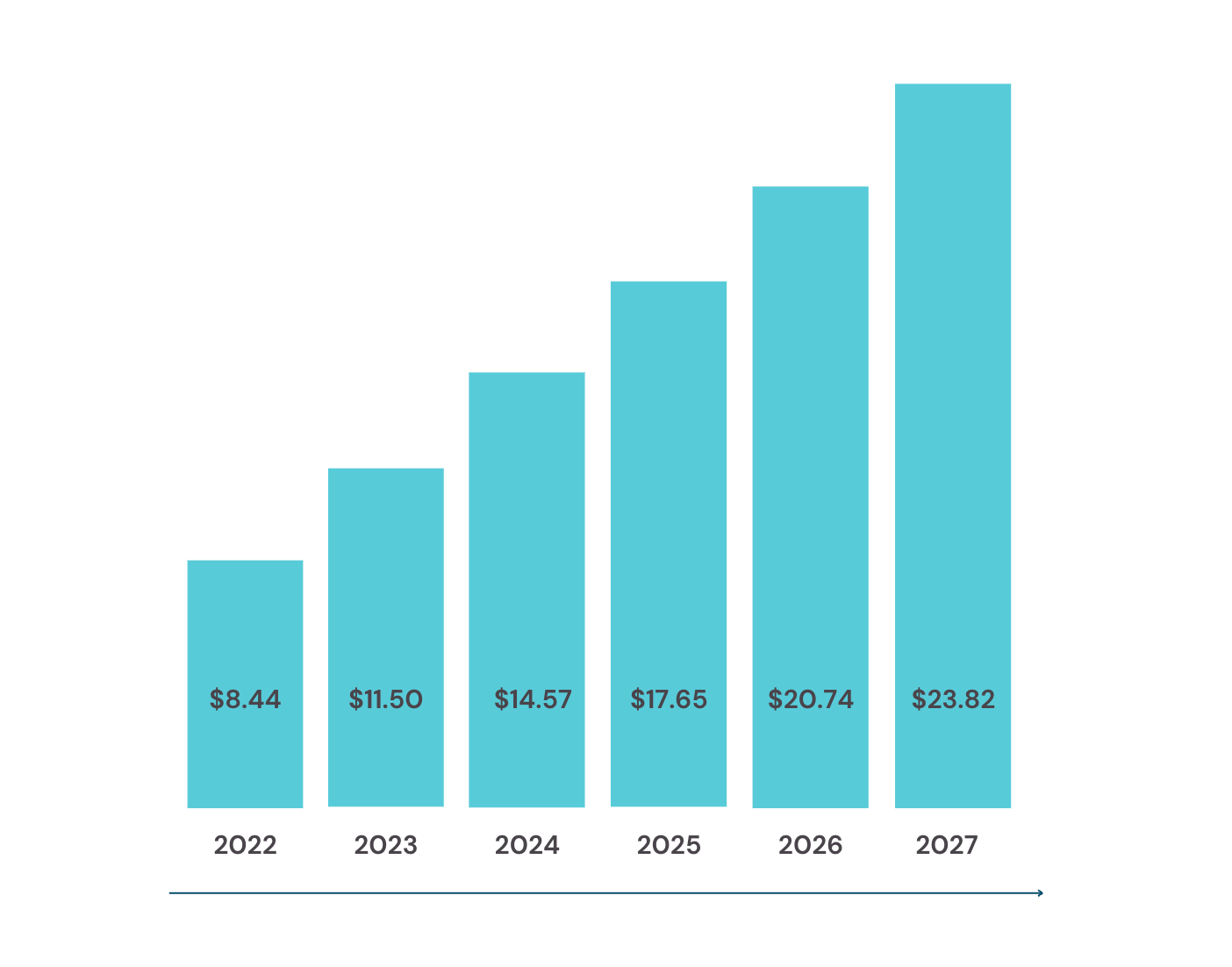
According to statistics, the cost of cybercrime is projected to skyrocket, with a significant surge expected in the coming years. Estimates indicate a staggering rise from $8.44 trillion in 2022 to $23.84 trillion in 2027.
The automotive industry is undergoing a significant transformation with the rapid integration of IoT technologies and the emergence of autonomous driving capabilities.
By 2025, the automotive IoT sector is projected to generate approximately $23.6 billion in revenue, accompanied by the presence of around 400 million connected vehicles and 80 million autonomous vehicles on the roads.
This transformative shift has not only revolutionized the industry but has also brought increased cybersecurity risks, making it a prime target for potential threats.
By prioritizing robust cybersecurity throughout the automotive ecosystem, the industry can embrace IoT benefits while ensuring the utmost safety and security for all stakeholders involved.
The CAN Injection: the most common attack
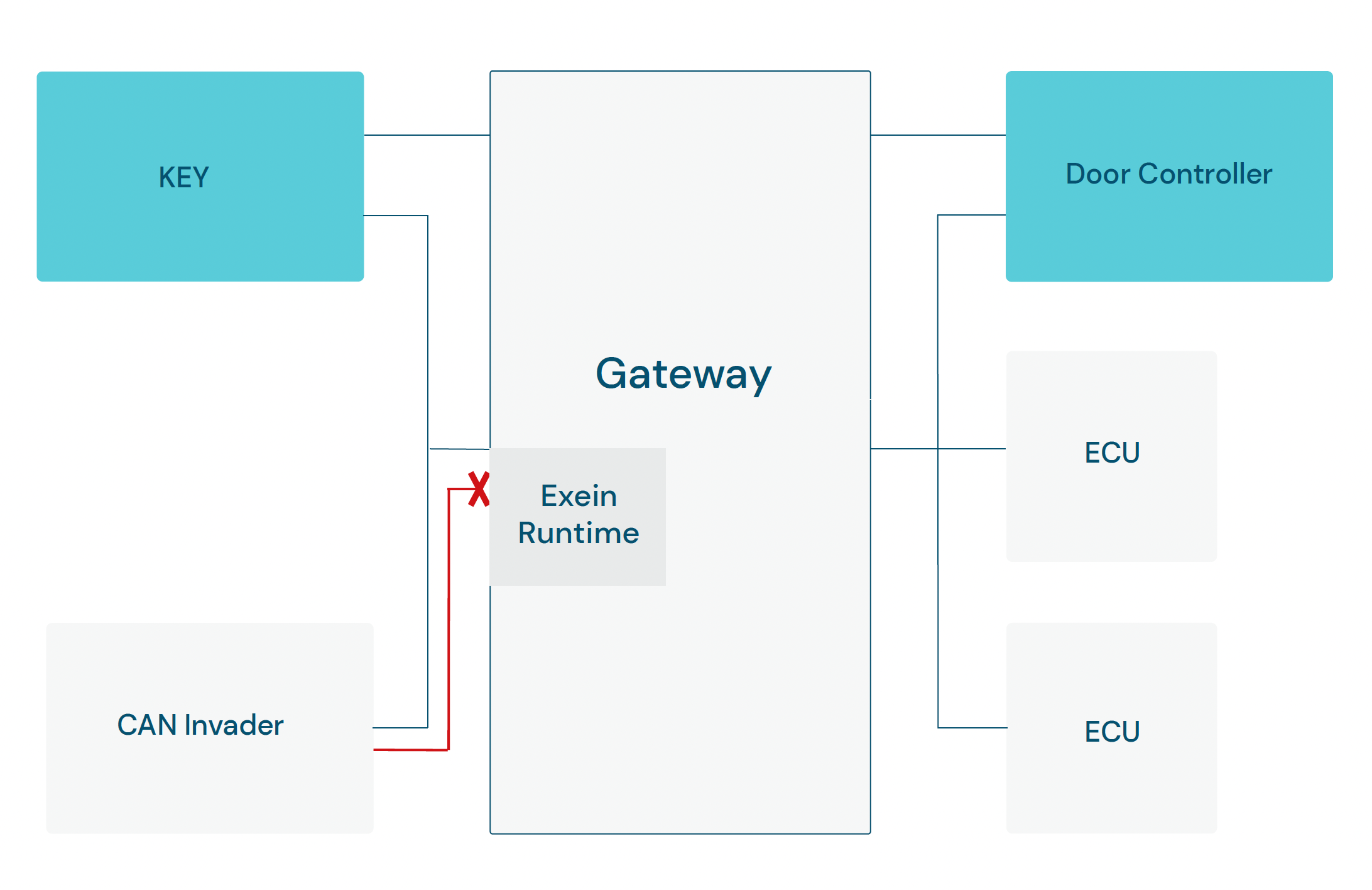
One of the most prevalent attacks on vehicles involves the use of a readily accessible device known as the "CAN Injection" or "CAN Invader". With this device, attackers can exploit vulnerabilities to gain unauthorized access to the Controller Area Network (CAN) bus. Once inside the vehicle's internal network, hackers can manipulate signals and breach the Electronic Control Units (ECUs), which control various critical functions such as doors, brakes, and more.
The CAN injection theft raises significant concerns for Original Equipment Manufacturers in the automotive industry. This is because the financial repercussions of having cars with a reputation for being susceptible to theft can be substantial, potentially resulting in adverse effects on sales and brand reputation.
What strategies can OEMs employ to counter these attacks?
One highly efficient and easily deployable solution is to implement Exein Runtime through a software update, eliminating the need for additional hardware or physical alterations.
This enables OEMs to enhance cybersecurity of existing vehicles without requiring modifications.
Depending on the vehicle’s architecture, our solution can be implemented either in a Gateway, stopping the propagation of the attack to the critical ECU, or in the critical ECU itself. The accompanying diagram showcases the effectiveness of Exein Runtime when positioned within the Gateway.
In this scenario, a simulated malicious message is intercepted and blocked by Exein Runtime before reaching any vehicle vital component.
EXEIN ENTERPRISE
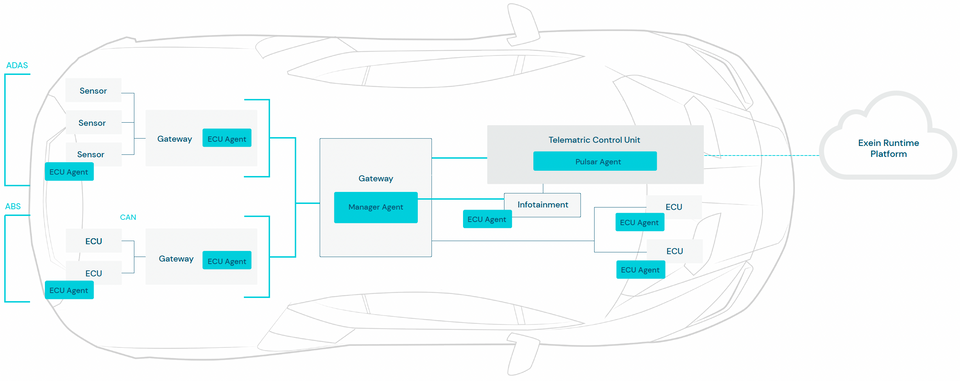
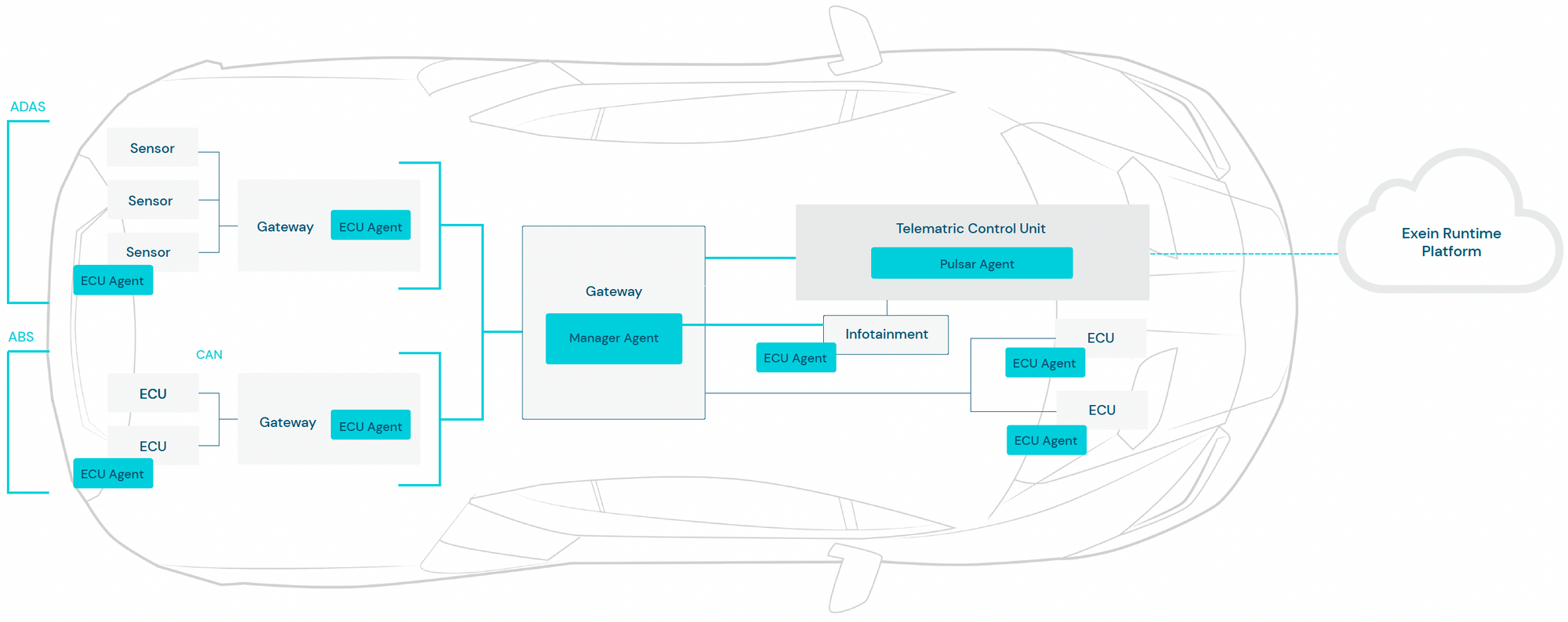
Our solution for the Automotive Industry is a comprehensive system that combines multiple components to ensure effective mitigation of attacks.
With its robust architecture, the solution incorporates the following essential elements:
a) Exein Platform
Exein Platform is our SOC for managing fleets of vehicles. It integrates processes, advanced SIEM technologies and a team of proficient experts.
It collects data transmitted from our Pulsar Agent and Manager Agent, displays it, generates a comprehensive report, and our experts manually analyze and send firmware updates to the vehicles fleet.
b) Exein Analyzer
Exein Analyzer is a cutting-edge solution designed to provide comprehensive firmware analysis. With its continuous monitoring and detection capabilities it guides vulnerability response throughout every stage of vehicle and component lifecycle, including development, production, and post-production.
As a highly advanced vulnerability detection system that operates continuously, it enables fast and prioritized vulnerability handling ensuring a comprehensive and up-to-date vulnerability profile.
c) Exein Runtime
Our Runtime security solution for the automotive industry includes several components. The Pulsar agent, which protects the host and communicates with the cloud-based platform; the Manager agent, responsible for collecting and forwarding data from the ECU agents to the Pulsar agent; and the ECU agents, lightweight monitoring agents that send data to the Manager agent.
Together they provide comprehensive monitoring and management of the entire automotive system and fleet, ensuring optimal performance and cybersecurity.
Our enterprise-class security solutions provide organizations with the right combination of monitoring, protection and response capabilities to reduce the risk of cyber attacks.
At Exein we recognize that every organization has unique security needs, which is why our solutions are customizable to meet those specific requirements.
If you are unsure about what’s the most appropriate solution for your company, our team of experts will work with you to understand your project requirements and provide a proof of concept (POC) that is entirely free of charge.
During the POC, we will discuss how our technology can help solve your security problems and provide an opportunity to see it in action.
Contact us at hello@exein.io